What is Behavioral Biometrics?
Behavioral biometrics analyzes unique micro-patterns in movement. It analyzes the way that a user types and moves their mouse to assure their identity. These patterns are unique and would be difficult to duplicate or used to impersonate the accurate user. It identifies an individual based on the way that they behave instead of the things that they know or their body parts. Behavioral biometrics authenticates continuously, monitoring a user’s behavior in real-time. It, therefore, increases security and can detect a compromised session as it happens.
Introducing Plurilock DEFEND™
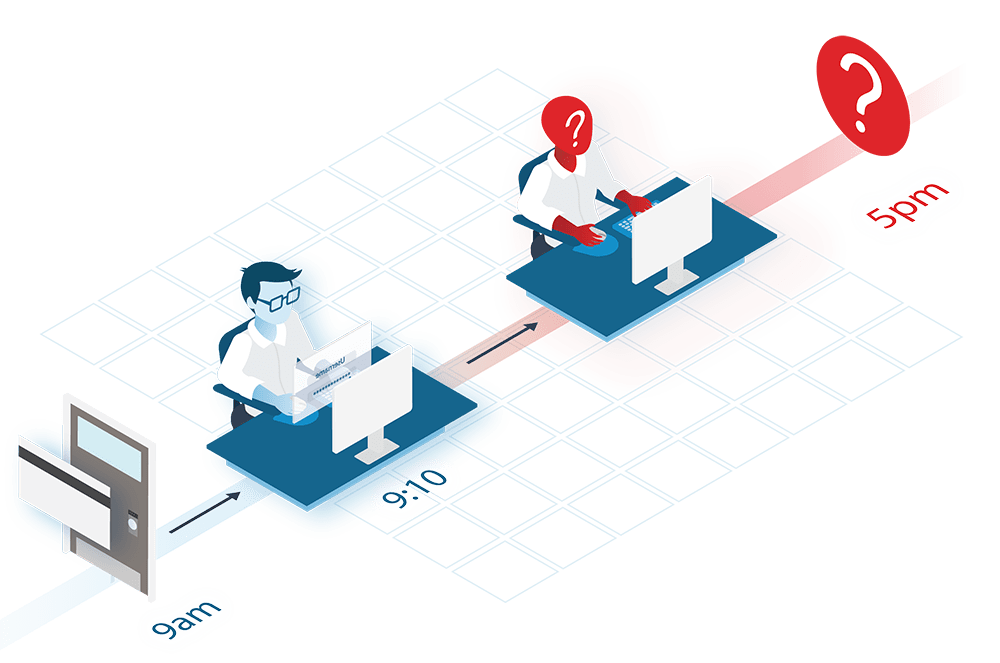
- DEFEND uses behavioral biometrics to identify users based on how they interact with their system
- DEFEND monitors mouse movements and keystrokes patterns to identify a user—no risk will be reported so long as a user’s movement matches their typical behavior
- Risk is reported immediately if a user’s behavior seems unusual or deviates from typical movement patterns, leading DEFEND to alert security staff of a potential identity threat